AAA and Defense in Depth
In this case study I’ll be taking a closer look at the LinkedIn data breach of June 2021. This case made the news because it was originally found on ‘RaidForums’ as a bulk selling lot for 700 million users (Mathews, 2021) or 92% of all users’ public data in a consolidated format only two months after a similar occurrence. A similar occurrence had a slightly smaller breach with 500 million users’ data becoming vulnerable (LinkedIn Update on 500 million, 2021). ‘RaidForums’ is a well-known data marketplace on the dark web where the user ‘Tomliner’ (Gibson, Townes, Lewis, & Bhunia, 2021) added onto the 500 million previously leaked data with an additional 200 million (LinkedIn Update on 700 million, 2021).
The scope of the data included users’ full names, email addresses, phone numbers, and physical addresses (Gibson, Townes, Lewis, & Bhunia, 2021). Since the data was not accessed from a protected system within LinkedIn but instead a public application programming interface (API) that exposed too much, we can assert that this incident was purely a data breach without a security breach (Norton, 2019). LinkedIn attempted to save face with their consumers by claiming this was not a data breach because the data was not sensitive personally identifiable information (SPII) but instead just personally identifiable information (PII) (Gibson, Townes, Lewis, & Bhunia, 2021). This assertion by LinkedIn did little to calm their consumers as these incidents were becoming more frequent.
LinkedIn was a target for multiple reasons. The first reason that a malicious acter may have singled them out was their robust public API. Their API allowed an attacker to gather user information in a conformed and easily accessible manner. While having an API for a data set can enhance a business model such as adding additional revenue streams it can add a significant room to your company’s attack surface. Another reason LinkedIn may have been targeted is for the desirability of their dataset. Tomliner added to this data by using other APIs such as Facebook. This aggregate made for a rich source of data worth $5000 per copy. This consolidated data could be valuable to other malicious actors, businesses as marketing leads, or to businesses for recruiting leads. The most unfortunate part of this incident and other data breaches like it is that once the data is public there is not much a company can do to ‘rollback’ its effects. This permanently damages the reputation of that company with its user base.
LinkedIn can implement the AAA security measures which include Authentication, Authorization, and Accounting. LinkedIn can enforce public API requests with a bearer token or some other form of authentication which enables LinkedIn to identify who is asking for information. Authorization can be implemented to ensure that only the data the user of the API is paying for is sent, which reduces the attack surface of the company. Finally, Accounting helps create a chain of custody of the data so they can enforce their terms and conditions on violating offenders with logs and verifiable proof.
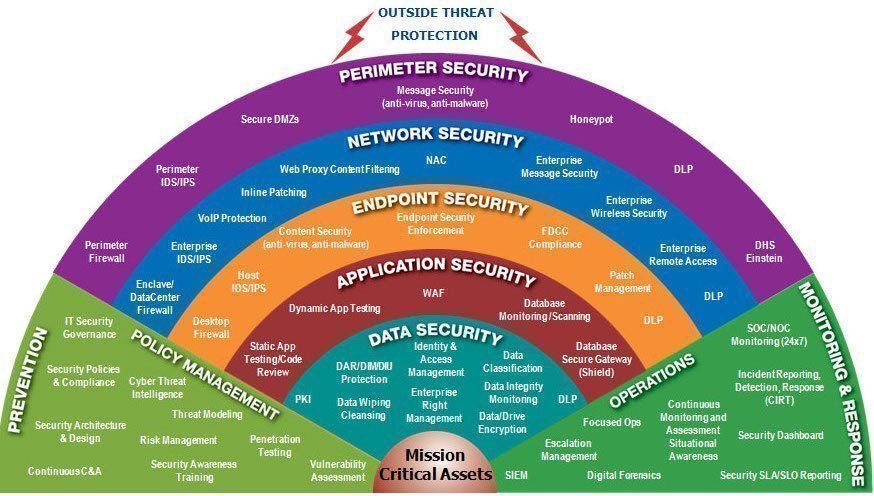
Immediate threats for LinkedIn would include ongoing access for malicious actors though their public API. As we’ve seen that their robust API is so enticing that malicious actors cannot resist it would indicate that the risk to reward ratio is favoring risk and no longer cost-effective to provide given the damage it causes. Some mitigation tactics that the LinkedIn team could deploy is to break their API into multiple paid accessible APIs and increase the overall price to query it. Finding the financial breakeven point for a bad actors’ motives can help discourage them from even attempting their efforts while preserving the service for more legitimate users. AAA security measures are one form of enforcement and need to be layers with others such as blocking high risk regions, blocking known VPN servers, and regular monitoring of the data accessed which may lead to audits for API users that are suspiciously overconsuming. By implementing multiple layers of security, you can create what is known as Defense-in-Depth (DiD).
References
- Gibson, B., Townes, S., Lewis, D., & Bhunia, S. (2021, December 15-17). Vulnerability in Massive API Scraping: 2021 LinkedIn Data Breach. IEEE. Retrieved from https://ieeexplore.ieee.org/document/9799221
- LinkedIn. (2021, April 8). An update on report of scraped data (500 Million). Retrieved from LinkedIn Pressroom: https://news.linkedin.com/2021/april/an-update-from-linkedin
- LinkedIn. (2021, June 29). An update on report of scraped data (700 Million). Retrieved from LinkedIn Pressroom: https://news.linkedin.com/2021/june/an-update-from-linkedin
- Mathews, L. (2021, June 29). Details On 700 Million LinkedIn Users For Sale On Notorious Hacking Forum. Retrieved from Forbes: https://www.forbes.com/sites/leemathews/2021/06/29/details-on-700-million-linkedin-users-for-sale-on-notorious-hacking-forum/
- Norton. (2019, September 5). What is a security breach? Retrieved from Norton: https://us.norton.com/blog/privacy/security-breach