Algorithm Ciphers
Cryptography is changing rapidly, and many considerations need to be made while selecting the appropriate method of securing data. In this post we are working with securing data at rest instead of in transit, as such we do not need to concern ourselves with TLS encryption suites in this post. The difficulty with encrypting data at rest versus data in transit is we do not have an industry standard method such as TLS/SSL (Oracle, n.d.). Data at rest has two categories to consider when evaluating its well-being which are digital attacks and physical attacks. Digital attacks could be a bad actor with intent to obtain the data through means such as using falsified or stolen credentials, copies of data moved to unsecure locations, or even ransomware attacks where the attacker may not care for the data itself but hold the data ransom for the intended recipients (Cloudflare, n.d.). Physical attacks could be from direct access to a hard drive either through theft or copying the content.
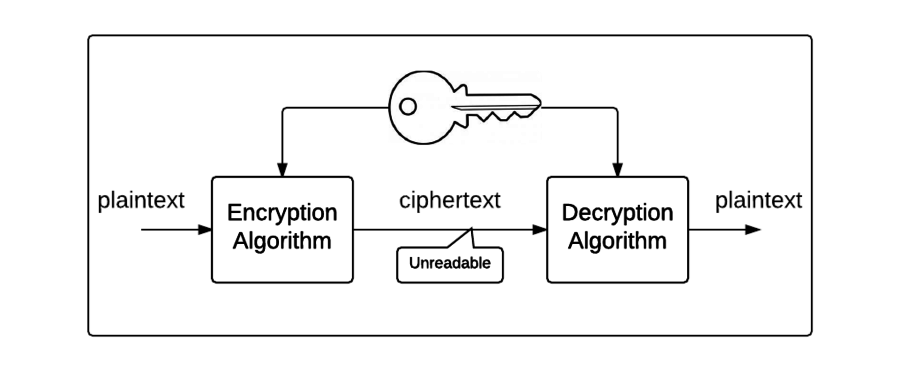
Some best practices to consider are secure the data physically such as a locked server room, locked sever cabinets, and drive encryption such as BitLocker by Microsoft. Drive encryption makes stolen hard drives useless because the data cannot be accessed without decrypting first with a private key stored on the TPM module of a motherboard. BitLocker uses a widely accepted encryption method called Rijndael algorithm better known as Advanced Encryption Standard (AES). AES can be used with three key sizes, 128 bits, 192 bits, and 256 bits (IBM, n.d.). Bitlocker, which is one of many drive encryption services provided, supports two of these three key sizes, 128 bits and 256 bits. By default, Bitlocker uses 128 bits, but I would recommend using 256-bit key size for increased security. The benefit of using a smaller key size or a less optimal encryption method is the speed in which data can be encrypted and decrypted but could be deficient when it comes to regulatory standards compared to the provided protection an AES 256-bit key size could provide.
Per the announcement of the AES encryption in the Federal Information Processing Standards Publication 197 we can see that there are currently no weak or semi-weak keys identified (NIST, 2001). If the private key were to become known to an attacker, the drive could be decrypted. The private key in drive encryption is typically stored in the TPM module of the motherboard which is tamper resistant (Microsoft, n.d.). The culmination of all these efforts, from AES 256-bit drive encryption to storing the private key in a tamper resistant module provided by hardware manufacturers allows for end-to-end protection from physical attacks on data at rest.
If an attacker could understand how a key is formulated, they could in theory recreate a private key to use for decryption. This is why generating random numbers is crucial for encryption. Many computers collect random information throughout various parts of the hardware such as voltage, temperature, etc. but the pool of various information sources is limited and thus generating a new key could be stalled while the system waits for an accumulation of new random information (Oracle, n.d.). This is in turn used in a cryptographic pseudorandom number generator (CPRNG) that captures a “seed” of random information and further generates data to the specified bit length. Platforms such as Java have built in classes that allow access to CPRNG algorithms. In Java, this class is referred to as ‘SecureRandom.’
The second form of attacks as mentioned before is digital attacks. While this data is not in transit, and if it were it would be encrypted with various TLS cipher suites, it could be accessed from bad actors that gained privileges inside a network to connect to a storage device. Considerations can be made to prevent such attacks such as only allowing internal devices or trusted devices to connect. Credentialling of users that should be able to connect remotely should be heavily monitored and restricted to users that have an absolute need for such an action.
Government regulations could include the Gramm-Leach-Bliley Act that requires financial institutions, such as Artemis Financial, to secure their data. To justify using AES 256-bit encryption we can turn our attention to how the United States Federal Government secures their classified data with AES 256-bit encryption (Wong, 2022). If the US government is leading the way with encryption and is using the same method recommended, we can assume it would be sufficient for the Gramm-Leach-Bliley Act regulatory standards.
References
- Oracle (n.d.). Java Security Standard Algorithm Names. https://docs.oracle.com/javase/9/docs/specs/security/standard-names.html#cipher-algorithm-names
- Manico, J., & Detlefsen, A. (2014). Iron-Clad Java. McGraw Hill Computing. https://learning.oreilly.com/library/view/iron-clad-java/9780071835886/?sso_link=yes&sso_link_from=SNHU
- Cloudflare (n.d.). What is data at rest? Retrieved August 4, 2024, from https://www.cloudflare.com/learning/security/glossary/data-at-rest/
- IBM (n.d.). Cryptographic algorithm and key length. IBM Documentation. Retrieved August 4, 2024, from https://www.ibm.com/docs/en/sgklm/4.1.1?topic=overview-cryptographic-algorithm-key-length
- Microsoft (n.d.). BitLocker FAQ. Windows Learn. Retrieved August 4, 2024, from https://learn.microsoft.com/en-us/windows/security/operating-system-security/data- protection/bitlocker/faq#what-form-of-encryption-does-bitlocker-use--is-it-configurable-
- National Institute of Standards and Technology (NIST) (2001). ADVANCED ENCRYPTION STANDARD (AES). Federal Information Processing Standards Publication 197. https://csrc.nist.gov/files/pubs/fips/197/final/docs/fips-197.pdf
- Microsoft (n.d.). What is TPM? Windows Support. Retrieved August 4, 2024, from https://support.microsoft.com/en-us/topic/what-is-tpm-705f241d-025d-4470-80c5-4feeb24fa1ee
- Wong, W. (2022, January 12). Federal government leads the way with encryption standards. Insights. Retrieved August 4, 2024, from https://insights.samsung.com/2022/01/12/federal-government-leads-the-way-with-encryption-standards/